Centralise identity data access governance
Gain granular control over which customer identity attributes can be accessed by internal and external applications

360 degree view
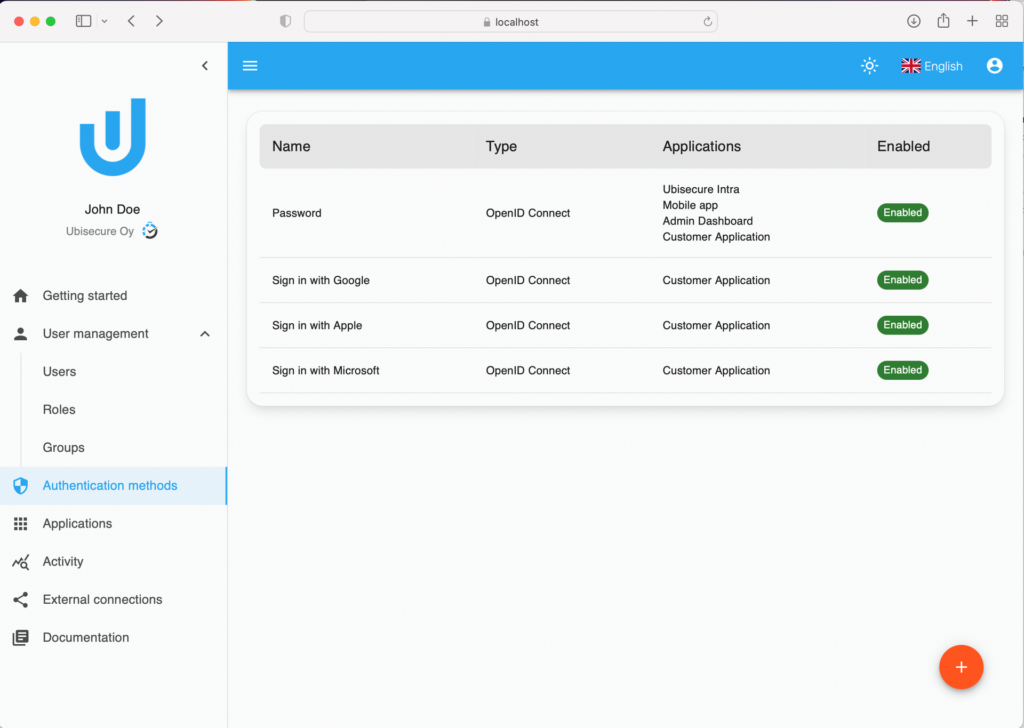
Manage how applications authenticate customers, organisations, things & APIs
Manage which customer identity attributes can be accessed
Centralised policy management
Control and audit how applications consume and share user attributes
Easily manage policy for user types based on commercial, corporate, security or regulatory demands
Role Based Access Control (RBAC) & Attribute Based Access Control
- Understand the system needs of your customers, group them into roles based on common requirements
- Build authorisation policies for applications and deliver the correct role and attribute to the target systems
- Expand beyond basic access control by incorporating access decisions based on sophisticated authorisation policies
- Support policies that evaluate the strength of the authentication method, time of the event, location, identity attributes, roles, operating system and the version, browser version and more
Identity Attribute Broker Engine
- Attributes can be aggregated from various sources, i.e. user database, CRM, 3rd party APIs
- Support user privacy with the minimal attribute set approach – gives you granular control over which attributes are sent to target applications
- Pseudonymisation of attribute names and values as needed by policy or regulation
DNA Telecom
Learn how the Ubisecure Identity Server was the key component for cloud brokering service, DNA Pouta, providing convenient access to DNA corporate customers, enabling DNA to standardise the integration of the selected cloud applications to the IAM infrastructure.
> > Read Case Study
Resources
ANALYST EXECUTIVE SUMMARY
By KuppingerCole
An overview of the Customer Identity and Access Management (CIAM) industry & an impartial high level description and analysis of the Identity Platform.
>> Read More
CASE STUDY

Deploying a nationwide identity management and delegation platform for citizens and businesses.
>> Read More